The development of QuickHash v3.0 continues as per my previous two announcements. But, as excited as I am about QH v3.0, I have other programming projects going on too, and one had been neglected for a while called ‘YAFFI’.
YAFFI is a disk imager that I first made for a bit of fun back in 2015 but it has since been left abandoned pretty much and I wanted to kick start its development again. Now, lets be clear here : this is not just a front end for an existing open-source imager! I wrote the thing from scratch!! It is months of work. So please do not assume it’s something I cobbled together while drinking a coffee and eating a Bourbon. It took a long time and is a fairly advanced bit of software really. Not as polished or as effective as the professional tools of course, and no where near the standards of X-Ways Forensics and the like. But for a free imager that anyone can use for both Windows AND Linux which also creates E01 forensic images with or without compression and with or without hashing, I’m pretty proud of it.
So for the last few weeks, alongside the late night development of QuickHash v3.0.0, I’ve been tinkering with YAFFI as well. The first port of call was to implement the wonderful hash library that I added to QH 2.8.0 called HashLib4Pascal which obviously helps me handle the hashing side of things. It’s such a good library and seeing as I have learned how to use it already for QuickHash, it was not a major problem adding it to my own disk imager YAFFI.
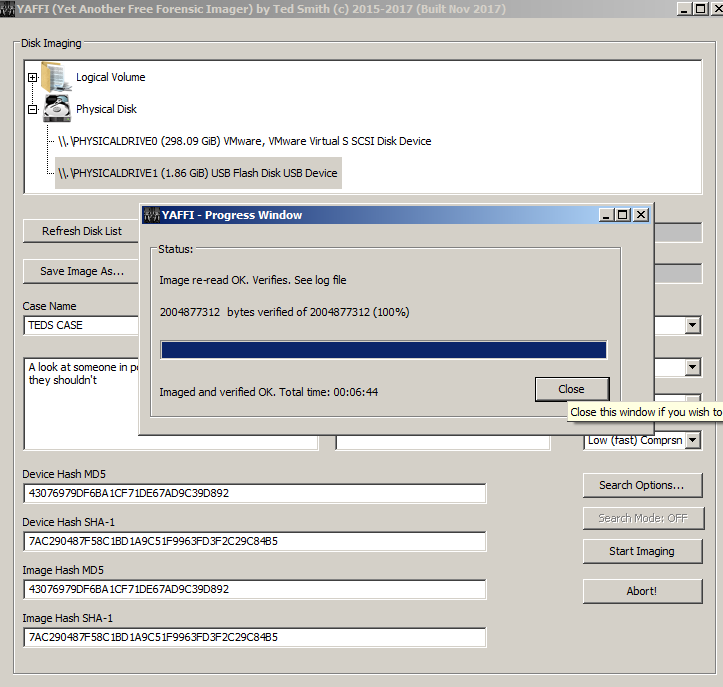
For now, I have just replaced the original hashing options (MD5, or SHA-1, or MD5 & SHA-1 combined) with the new library, just to make sure I have implemented it OK. But assuming that has all gone OK, I can then easily add SHA256 and SHA512 and whatever else we want.
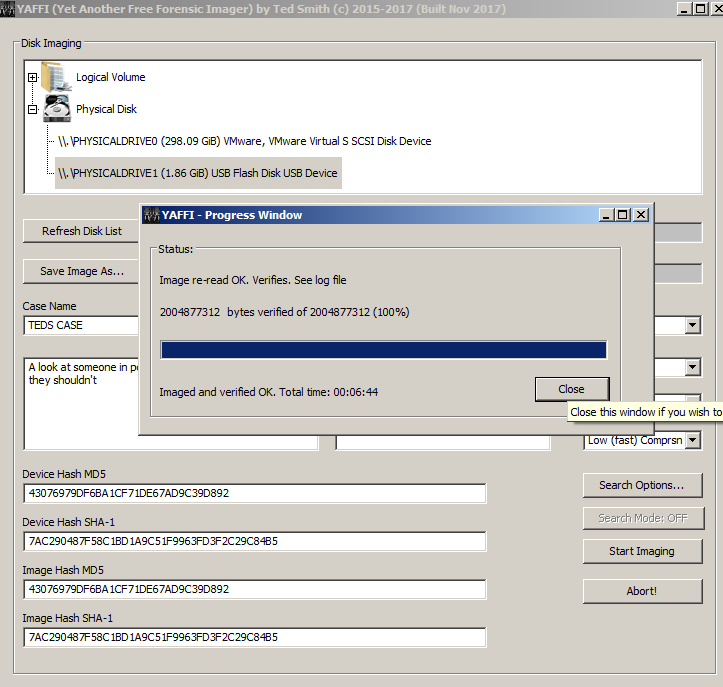
It’s worth pointing out that YAFFI can create valid E01 images that top end commercial tools are happy with. For example, as you can see below, an image I created of a USB drive has been opened by X-Ways Forensics without complaint.
In addition, YAFFI is now set to recognise the GUID’s of Apple APFS formatted drives, so if you right click such a drive and ask YAFFI to show you technical disk specifications, it should tell you that it is APFS formatted even before you have imaged it.
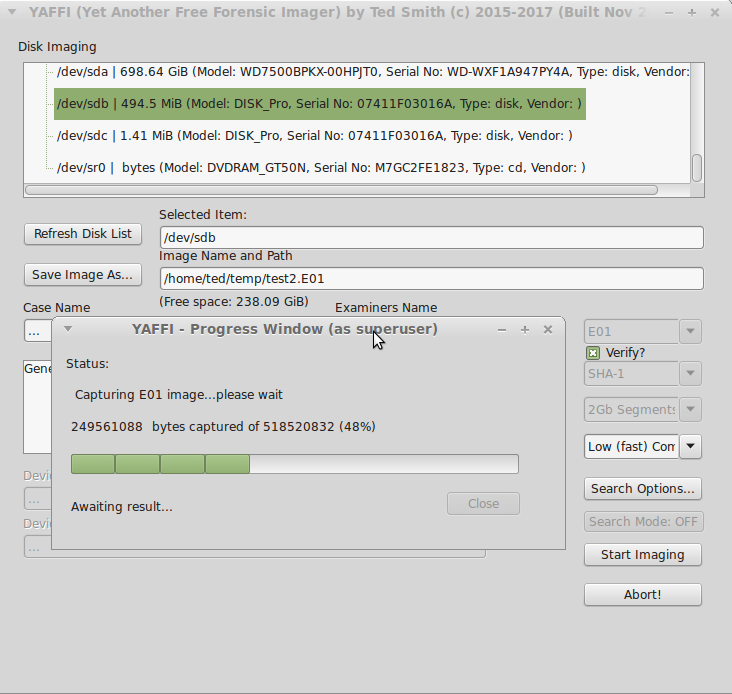
Don’t forget this imager was designed for Linux primarily, to allow the creation of E01 images on the Linux platform. As you can see below, it works and looks pretty good :
I’ve also added a logical drive volume wiping facility. This seems strange for a disk imager, I admit. But it’s a question I get asked a lot with data security in so many peoples minds these days: “When I throw my computer out, how can I wipe my drives”. Well YAFFI will allow you to do this at zero cost. Basically, after launching YAFFi as administrator or with administrative rights, you right click the drive you wish to wipe from the ‘Logical Drive’ section (e.g. Drive X:) and choose Wipe Drive in the dragons lair sub-menu. Accept the “Are you really sure” confirmation box and the partition will be zeroed to 0x00. The screenshots below illustrate.
Before
During the wiping process:
After disk wiping:
All of that said, lets be realistic…this is a tool I developed at home using mostly virtual machines and one Linux computer. There is a limit as to how many variants I can forsee so I do expect some of you to report problems with access or things failing half way through. For now, YAFFI should be used for tasks that are not life and death, like the occasion where your computer does a Windows update and then fails to boot so you want to image it before you do anything else. It shouldn’t be used as part of a criminal prosecution case yet because there may be things I am not yet aware of; in fact I’m sure there will be. For now, it’s something to have fun with and perhaps get interested in as a project that can be developed collaboratively in the future.
https://github.com/tedsmith/yaffi/releases
The YAFFI page is currently on GitHub at www.github.com/tedsmith/yaffi and the pre-compiled binaries for Windows and Linux are available at www.github.com/tedsmith/yaffi/releases


Leave a Reply